Tag Search: security
Posted on Thursday September 13, 2018 | bitcoin, crime, security
An anonymous reader quotes a report from ZDNet: Users of Kodi, a popular media player and platform designed for TVs and online streaming, have been the targets of a malware campaign, ZDNet has learned from cyber-security firm ESET. According to a report that will be published later today and shared with ZDNet in advance, the company's malware analysts have uncovered that at least three popular repositories of Kodi add-ons have been infected and helped spread a malware strain that secretly mined cryptocurrency on users' computers. ESET researchers say they found malicious code hidden in some of the add-ons found on three add-on repositories known as Bubbles, Gaia, and XvBMC, all offline at the time of writing, after receiving copyright infringement complaints. Researchers said that some of the add-ons found on these repositories would contain malicious code that triggered the download of a second Kodi add-on, which, in turn, would contain code to fingerprint the user's OS and later install a cryptocurrency miner. While Kodi can run on various platforms, ESET says that the operators of this illicit cryptocurrency mining operation only delivered a miner for Windows and Linux users. The crooks reportedly mined for Monero, infecting over 4,700 victims and generating over 62 Monero coins, worth today nearly $7,000.

Posted on Tuesday September 04, 2018 | web and cloud, security, scalability, hybrid cloud, cloud computing
 Cloud computing has become an indispensable component in business IT because it's cost-effective, flexible, and secure. Thanks to hybrid cloud solutions, organizations have access to even more agile computing resources.
Cloud computing has become an indispensable component in business IT because it's cost-effective, flexible, and secure. Thanks to hybrid cloud solutions, organizations have access to even more agile computing resources.

Posted on Thursday August 30, 2018 | smartphone, security, malware, cyber crime, android
 Smartphones are like palm-sized computers, and they deserve the same protection as desktops and laptops. While you don't need to install bulky security software to protect against cyberthreats, there are steps you can take to keep cybercriminals at bay.
Smartphones are like palm-sized computers, and they deserve the same protection as desktops and laptops. While you don't need to install bulky security software to protect against cyberthreats, there are steps you can take to keep cybercriminals at bay.

Posted on Monday August 27, 2018 | sharepoint, security, scams, phishing, outlook, office 365, microsoft, cyberattack
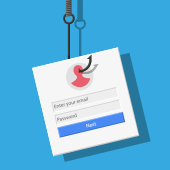 Phishing scams disguise malicious links and emails as messages from trusted sources. The most recent scam to watch out for almost perfectly imitates a trusted invitation to collaborate through Microsoft SharePoint. It's a three-step attack that's easy to avoid if you know how it works.
Phishing scams disguise malicious links and emails as messages from trusted sources. The most recent scam to watch out for almost perfectly imitates a trusted invitation to collaborate through Microsoft SharePoint. It's a three-step attack that's easy to avoid if you know how it works.

Posted on Tuesday August 14, 2018 | virtualization, security, risks, patches, management, infrastructure, audit
 While virtualization security is often viewed as an afterthought, it is nevertheless important. Like all technology, securing your virtualized infrastructure is vital to your business's success. Let's take a look at some of the security risks posed by virtualization and how you can manage them.
While virtualization security is often viewed as an afterthought, it is nevertheless important. Like all technology, securing your virtualized infrastructure is vital to your business's success. Let's take a look at some of the security risks posed by virtualization and how you can manage them.

Posted on Friday August 10, 2018 | voip implementation, voip for business, voip, telecommunications, security, network stability, internet phone call
 Companies that want to stay ahead of the curve are switching to Voice over Internet Protocol (VoIP) solutions to drive productivity and mobility. To get ready for the upgrade, you need proper planning and network preparation -- here are the most critical considerations.
Companies that want to stay ahead of the curve are switching to Voice over Internet Protocol (VoIP) solutions to drive productivity and mobility. To get ready for the upgrade, you need proper planning and network preparation -- here are the most critical considerations.

Page: 1234567891011121314151617181920212223242526272829303132333435363738394041424344454647